The retirement of Technical Debt has never been more relevant. The great recession, and, more recently, the COVID-19 pandemic have significantly dampened the ability and willingness of enterprises to address an ever-growing amount of Technical Debt. Too often, businesses have delayed or reprioritized initiatives intended to inject new technology into the IT footprint, creating a situation of low performance and innovation.
However, there is some good news on the horizon. As the practice leaders for Application Modernization at Converge Technology Solutions, we have seen signs of change and an increasing level of demand for our services over the past six months. It appears that organizations are now finally planning to update their aging IT investments.
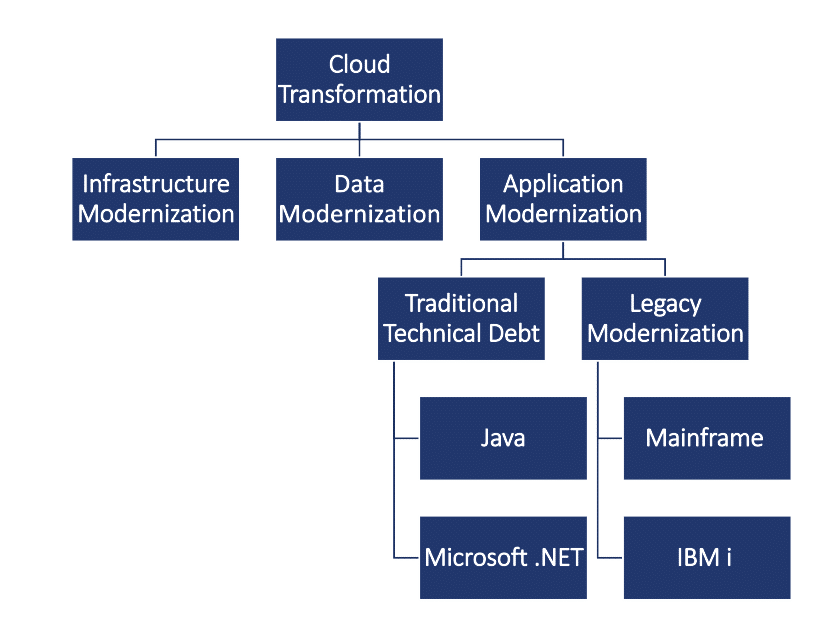
As the graphic below shows, any large-scale cloud transformation initiative will encounter needs to modernize infrastructure, data, and applications. These three areas are not independent. They instead are intimately connected; Applications act on data and live on infrastructure, whether that means deployed on-premise or to the Cloud. Not surprisingly, the problem can be broken down further. IT organizations must tackle Technical Debt that stems from their investments in stale Java and Microsoft technologies as well as Technical Debt associated with legacy systems such as mainframes.
One thing is for sure: leaving the status quo is not a good option. As we’ve previously explored, Technical Debt has the unfortunate potential to hurt both company image and customer relationships. There is a lot of work to do. Let’s look at how to succeed in addressing Technical Debt through application modernization.
Succeeding with Application Modernization
The path to successful large-scale application modernization can be fundamentally broken down into two steps: formulation of a vision and the design and execution of a program that diligently realizes that vision.
Vision
Enterprises must think big and bold. They must think big in Google’s 10x big sense. For the goal to be truly transformative, a new vision must push the envelope and challenge most aspects of the status quo. This vision must lay foundations with implications that impact both short and long-term business horizons. To realize such a vision, enterprises must design a comprehensive program that will cover people, processes, and technology. On the technology front, innovation and true modernization will emerge when holistically all aspects of IT are considered – a theme which was explored in our post on Cloud IT.
Program
Any non-trivial vision will require different types of effort. There will be activities in the form of experiments and trials. These can be technology-based or related to changes in process. On the technology side, expect to run experiments that validate hypotheses. These experiments are often in the form of proofs of technology (PoT) or proofs of concept (PoC) where you test design ideas, process changes, or even team restructuring. A program will be based on a very comprehensive set of projects that together help bring your vision to fruition. It will most likely include modernization and statements relating to the structure, management, and governance of the next-generation data layer. To deliver new value, programs will have to carefully account for customer preferences, and often, a trade-off will have to be made to properly prioritize between competing and similar requirements and feature sets. Kano-based analysis may come in handy to understand and rate customer-centric valuation against internal business imperatives and success criteria.
Given the importance of data analytics, if a program does not include activities focused on capturing and incorporating insights, performance, and real-world customer feedback, then rest assured that your program will be missing a critical element and your mileage will definitely vary.
Let’s look at the four-step process that leads to a bold vision and a solid program.
1. Assess
The process starts with an assessment of your inventory of IT assets and investments. These include both custom and off-the-shelf components, often deployed on-premise and in the public cloud. As part of the discovery process, geographical, governance, and compliance considerations must be factored in. The assessment also needs to discover and evaluate the economic details of the current IT footprint and skill set reality to account for labor market impact. Be prepared to conduct multiple interviews with the appropriate stakeholders and subject matter experts. Lastly, let’s not forget the market and competitive landscape. If not promptly addressed, your weaknesses will be exploited.
The outcome of this first phase is a vision for the future gained through critical and strategic thinking.
2. Plan
Once all data points are collected, the process moves into an analysis phase. This is where priorities and dependencies are determined. It is an exercise of trade-offs against costs, time, and value delivery while imparting a strong set of constraints stemming on a technical level. The program will identify PoCs, PoTs and help validate or dispel ideas and hypotheses. Programs should also provide a sense of how projects and smaller initiatives relate to each other and their technical prerequisites.
The outcome includes a high-level roadmap, and a cataloged set of projects and subprojects waiting to be executed. The program should be phased, regardless of the extent. Often the early stages involve remediation actions and fulfillment of prerequisites. They are foundational and generally lead to smoother sailing.
3. Migrate
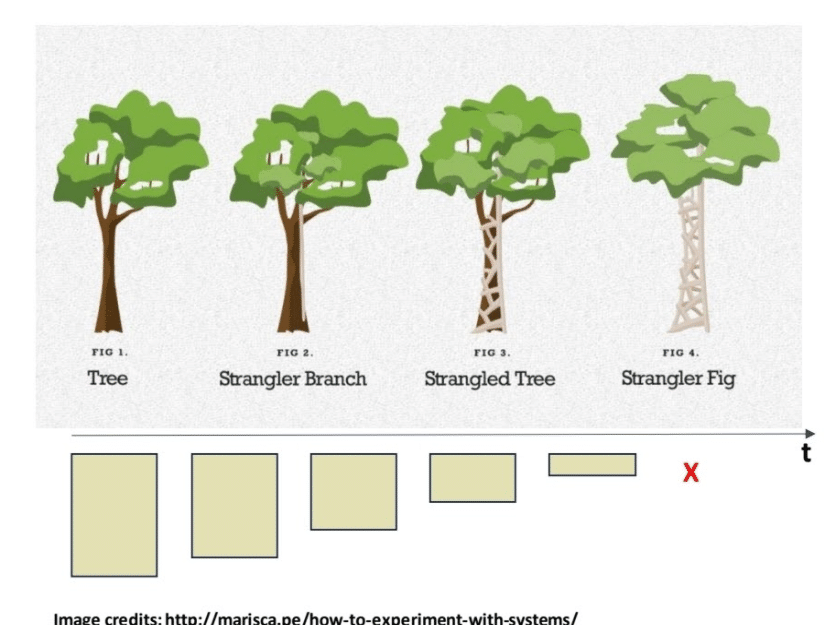
Migration is an overloaded and often multi-sense word. Within the context of a well-formed modernization program, migration will apply one of the now customary six R’s. Non-trivial programs will find that in practice a strategy mixture of rehosting (lift and shift), refactoring/rearchitecting, and re-writing will be used. This implies that a mixture of old and radically new skill sets must be part of your team structure in order to succeed. Non-trivial programs are usually multi-year, as it is rare that older systems are decommissioned in a snap. Often bridges between the legacy and the new need to be built to support the transition. We have found that these bridges are essential to maintaining compatibility with older systems in which new components are being built and deployed. The reader can think of this as a form of “strangler pattern” to use a term out of the Microservices world, applied to coarse grain projects underlying a larger scale program.
Through carefully planned and monitored execution, the program will lead to an outcome of migrated assets and a transformed enterprise.
4. Optimize
Conceived as an iterative endeavor, the program needs to account for many iterations of optimization. Technology will not stand still. System architectures will always have room for improvement. Within a cloud context, the choice of using or not using cloud-native, managed services will always be present. Does one build or delegate to the cloud service provider or third party? Does it make sense to adopt a SaaS-aligned strategy, effectively delegating most of the development and operation of the platform or component to an external entity? These are key questions that impact how far your optimization effort can go once you have landed in the cloud.
What’s the outcome of this phase? A system and culture of continuous improvement that drives innovation. Isn’t this what all CIOs strive for?
Conclusion
If our insights are correct, then this is the time to start your application modernization journey. Follow a structured program that will allow you to come up with a bold vision, and then realize that vision with conviction and a strongly validated process. Simply put: Migrate to Modernize.
About the Author
Michael “Mick” Bisignani, a professional technologist, has held CTO and IT director positions. In his spare time, Michael aspires to become a burgeoning chef. You can follow him on Instagram @micksterct to tempt your taste buds




