I woke up early and prepped to drive into enemy territory.
This past Friday, I made the drive up to Huntsville, TX, for the Huntsville Educator Security Luncheon. Patrick Vardeman, head of Cybersecurity Business Development at Converge, was invited to give a presentation, The Silent Threat to Your Business, focused on cybersecurity threats and best practices for better preparing against them. Coming from the Accudata acquisition, this was my first event as a new member of Converge’s event marketing team. However, when accepting the new role, I had no clue my first event would be an hour away from home and just two blocks down the road from the campus of my alma mater’s number-one rival school, Sam Houston State University!
Through the sea of orange flags, Bearkat paw prints, and SHSU car stickers, my lone Stephen F. Austin State University sticker in the shape of Texas on my back window was completely out of place.
Nevertheless, I had a job to do.
Dressed in my gray shirt, instead of the purple one I was warned not to wear, I pulled into Huntsville’s City Hall Café and Pie Bar and secured a table to display Converge brochures, pens, and surveys. I finally got to meet the other members of the Converge team for the first time since Accudata was acquired early this year. About 30 minutes later, the room began to fill with IT professionals from nearby school districts and other education industry avenues before the presentation began.
The presentation nailed in the fact that cyber threats continue to pummel the US every day and show no sign of stopping. These threats target both the public and private sectors, including this audience in the education industry.
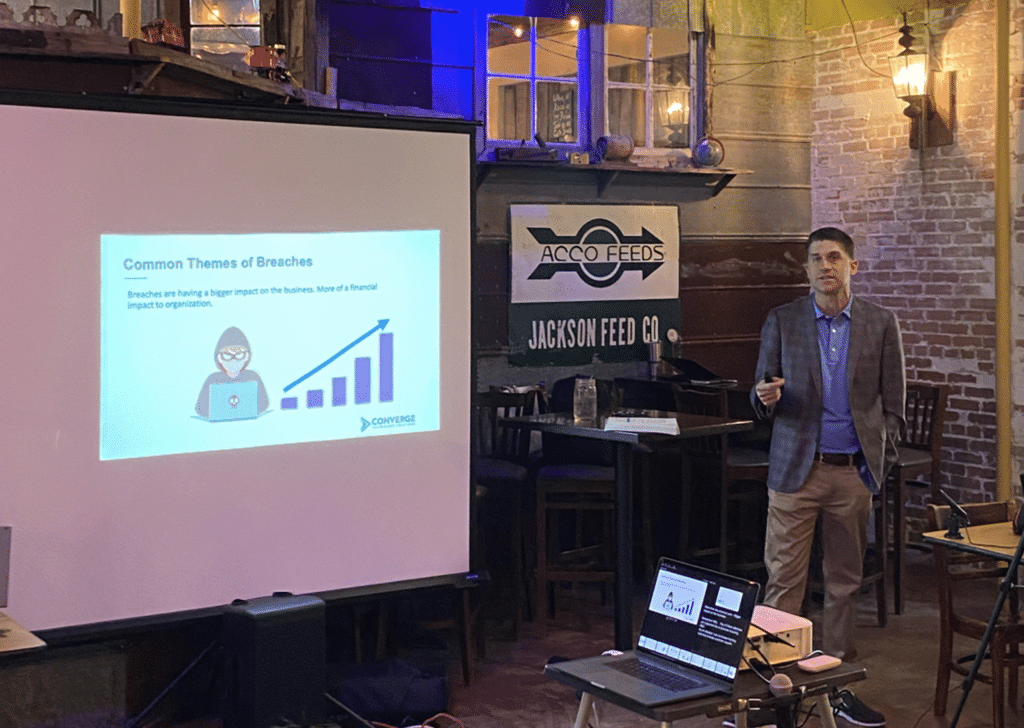
With the huge shift to remote work in response to the pandemic, 2020 became the biggest year for breaches. In education specifically, school districts had to deal with class invasions, denial-of-service attacks, and another level of ransomware that hadn’t been as big of an issue before. A record 408 cyber attacks toward K-12 school districts were publicly disclosed, according to the K12 Security Information Exchange.
The message that businesses must get prepared now for a potential cyber event was reinforced through real-life email compromise, insider attack, and ransomware breach stories that happened within the past year.
The crowd got involved by asking questions about multi-factor authentication (MFA). The concern was that it creates an extra step for the user, which could be seen as excessive and inconvenient. Patrick gave the following example of personal banking information to express to users the importance of MFA: “Would you feel comfortable with your retirement or banking accounts not having MFA or just one barrier to full access? It’s important to have that same feeling of wanting to protect sensitive business information, as data is the lifeblood of your business.”
The presentation wrapped up by suggesting the following immediate and strategic actions organizations should take to stay secure:
Immediate actions
- Rotate all passwords older than 90 days.
- Implement MFA for O365.
- Enable security access audit logs for critical systems and applications.
- Identify an organization to contact in breach.
- Verify your backups: Scope/timeframe/test.
Strategic actions
- Develop and test your incident response plan.
- Remove privileged access from standard users.
- Implement central logging and alerting.
- Consider managed security monitoring and response.
- Build and execute a cybersecurity plan.
As slices of pie were distributed across the room, attendees mingled amongst themselves before slowly making their way out.
Upon collecting surveys, I made my way out as well. But before heading back to Houston, I had to make a stop in the SHSU campus just to prove to myself that Stephen F. Austin reigns supreme as the best-looking school in the Piney Woods.
It does.
I put on my playlist of Jeremy Zucker, Christian French, Alexander 23, and Rence songs, hopped on I-45 South, waved bye to the giant Sam Houston statue on the side of the road, and enjoyed my hour-long drive back home to Houston.
With nearly all surveys rating the presentation 10/10 on the given scale and checking off that the information was “extremely helpful,” I would call the event a success! One attendee even requested a part two of the presentation for even more cybersecurity tips. Converge strives to host, plan, or collaborate with others on informative and useful events such as this one. For a full list of upcoming events, see our calendar.




