The Diners Club card was first issued in 1950 and heralded the beginning of the payment card industry (PCI). Cybersecurity became necessary for all transactions when the original carbon-copy impression payment slips evolved to magnetic stripes, EMV chips, and contactless and electronic payments.
To ensure a global data security standard, key stakeholders from major card brands (Visa, MasterCard, American Express, Discover, and JCB International) formed the PCI Security Standards Council (PCI SSC or the Council) in 2006. The PCI SSC sets the data security standard (DSS) for organizations that process, store, or transmit credit card and cardholder information.
Standard version 3.2.1 has been in place since early 2018. A lot has changed since that release, including an increase in online payments and the hyper-speed digital transformation caused by the global pandemic. Business networks are rapidly transitioning from traditional routers, switches, and servers in on-prem data centers to containers hosted in the cloud.
Digital transmission of cardholder data has inherent and ever-evolving risks throughout the payment life cycle, so the Council continues to evolve the PCI DSS to meet modern data protection needs. PCI DSS version 4.0 goes into effect on March 31, 2024, and has 63 new requirements. Some requirements are effective immediately, but the bulk isn’t effective until March 31, 2025, giving businesses a year-long transition period to implement the more challenging requirements.
While it’s true that the best time to prepare for v4.0 was last year, the second-best time is right now. And, yes, it is possible to get it all done even if you are starting now.
Our PCI compliance experts put together the following high-level guide to planning and prioritizing your efforts to achieve compliance when the deadlines hit.
What’s new in PCI DSS 4.0
The Council’s goal of bringing the PCI DSS standard up to date with current technologies and threats means revising authentication requirements—including broadening the required use of MFA and increasing password length to 12 characters—and extending the scope of the standard to include mobile, IoT, and cloud.
New requirements also address phishing, social engineering, and evolving attacks against e-commerce payment applications.
An added option allows businesses to develop a customized approach to meet the standard requirements. A bespoke approach can benefit large enterprises that want to use new technologies that can’t be tested through the traditional, defined method. However, the time, resources, and budget needed for self-testing will have most organizations sticking with the traditional, defined method.
The new standard emphasizes roles, responsibilities, and documentation, including enhanced reporting requirements, more than the previous standard.
Version 4.0 is a wide-ranging update, so these are just a sample of the more notable changes.
Prioritize and roadmap your PCI DSS v4.0 updates
Of the 63 new requirements, 13 must be met by the first deadline of March 31, 2024. The first round of updates generally requires low effort to address. The remaining 50 are enforceable on the same date a year later and can each take one to six months.
The chart below estimates the effort needed to meet each new requirement and the corresponding deadlines, grouped by PCI DSS section. Thirteen of the 2024 deadline requirements require low effort. However, 25 new requirements are considered high effort, likely requiring people, process, or technology changes that can take up to a year to implement. You can use this information to create a remediation timeline that helps your organization meet the necessary milestones and cross the finish line by the 2025 deadline.

Getting started
The impact of the new requirements will vary by organization, depending on the unique aspects and complexity of the environment. People, processes, and technologies will be affected, and additional documentation is required.
Organizations with complex or disparate technology stacks serving payment processes will likely be impacted most by the new requirements. Similarly, organizations with many PCI in-scope human resources or non-centralized processes will find meeting the requirements more challenging than other organizations.
Assessing the potential impact on your organization can help you maximize the runway available before the new standard is in place. Conduct a gap assessment as soon as possible and before the end of Q2 2023 so that action plans and compliance roadmaps can begin.
What you learn from a PCI DSS v4.0 gap assessment
The transition to PCI DSS v4.0 will take time. A structured gap analysis helps identify where your current environment aligns with upcoming requirements and where additional steps are needed to comply. The Converge PCI DSS 4.0 Gap Assessment helps focus, prioritize, and roadmap the remediation approach,
Our gap assessment provides a defined path to bring your organization into compliance by the deadlines.
We can help you complete the Attestation of Compliance (AoC) or Report on Compliance (RoC) as a Qualified Security Assessor (QSA) for over 15 years and delivered by Converge’s Accudata Systems.
This timeline example visualizes the value of doing a PCI version 4.0 gap assessment as soon as possible to identify what should be done now, next, and later for a prioritized approach.
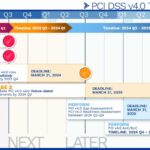
Do now – No later than the end of Q2 2023
- Perform a PCI v4 gap assessment
- Develop a PCI v4 remediation plan
Do next – Q3 2023 to Q1 2024
- Before Q4 2023: Remediate new phase 1 requirements
Deadline: March 31, 2024 - Before Q3 2024: Remediate future-dated phase 2 requirements
Deadline: March 31, 2025 - Before Q2-Q4 of 2024: Perform a follow-up gap assessment to validate compliance
Deadline: March 31, 2025
Do later – Q4 2024 to Q4 2025
- Complete AoC/RoC
How hard does it get?
The PCI SSC provides a filterable, sortable, prioritized list in a downloadable Excel file and a pdf document. New moderate and high-effort requirements are summarized below:
- 3.3.2: Encryption of sensitive authentication data (SAD) is required if it is stored before authorization is complete. This impacts cloud queuing services and point-of-sale processing devices.
- 3.3.3: (Issuers only.) Storage of SAD is limited to what is needed, secured, and encrypted with strong cryptography.
- 5.4.1: Additional processes for detecting and protecting personnel from phishing attacks must be implemented.
- 6.4.3: Requires management of all payment page scripts loaded and executed in the customer’s browsers.
- 8.3.6: Password length must now be a minimum of 12 characters.
- 8.3.10.1: (Service providers only.) If authentication is password/passphrase only, then it is required that these passwords/phrases are changed every 90 days.
- 11.3.1.2: Internal vulnerability scans must be performed by authenticated scanning.
- 11.4.7: (Multi-tenant service providers only.) Support is required for customers’ external penetration testing.
- 11.5.1.1: (Service providers only.) The use of techniques to detect or prevent intrusion is required to detect, alert, prevent, and address malware communication.
- 11.6.1: Mandates deployment of mechanisms to detect changes or unauthorized modification of consumer-based HTTP headers and payment pages.
- 12.3: A targeted risk analysis is to be performed for any new PCI DSS requirement.
- 12.5.2: The in-scope environment is to be validated every 12 months and with any significant change to the environment. This is an internal process separate from the one performed by a QSA.
- 12.5.2.1: (Service providers only.) Documentation and confirmation of the PCI DSS scope must be done every six months and with any significant change to the environment.
- 12.5.2: The in-scope environment is to be validated every 12 months and with any significant change to the environment. This is an internal process separate from the one performed by a QSA. You can learn more here.
What’s at risk without compliance?
There is a financial impact for organizations that don’t meet the requirements of PCI DSS v4.0 by the deadline. The Council has a fine structure based on the months an organization is out of compliance, with amounts increasing by tiers.
Because the standard intends to evolve security and limit risk for everyone on the payment chain—especially consumers—out-of-compliance practices can be a red flag that indicates uncorrected vulnerabilities and increased risk. So along with fines, non-compliant merchants may lose essential contracts needed to continue to accept card payments. Similarly, merchant service providers may lose key business relationships due to non-compliance with PCI v4.0.
Compliance is a continuous process
The changes looming for PCI DSS v4.0 can seem daunting, but Converge has a skilled team with more than 15 years of PCI experience ready to guide your organization on the best path for compliance for your organization.
We also offer a complete lineup of other PCI compliance services to help you test, attest, and support your compliance objectives. Contact us today to get started.
Related Topics You Might Be Interested In
PCI DSS v4.0 Deep Dive: Scoping Requirement 12.5.2
PCI Compliance: SAQ A Changes With Big Impact for eCommerce Sites